Version 23.241 of FileCloud has dropped support for Shibboleth 1.3 and SAML 1.1, and updated SimpleSAML to version 2.x. If you upgrade from a version below FileCloud 23.241 and your FileCloud build uses SSO, follow the instructions in Configuring SSO after updating from a version older than 23.241 in Windows: Upgrading Versions <23.242 to the Latest Version or Linux: Upgrading Versions <23.242 to the Latest Version or SSO will not work correctly in your system.
Note: As of FileCloud Version 20.3.2, to achieve high availability, you can configure FileCloud to support multiple memcache servers.
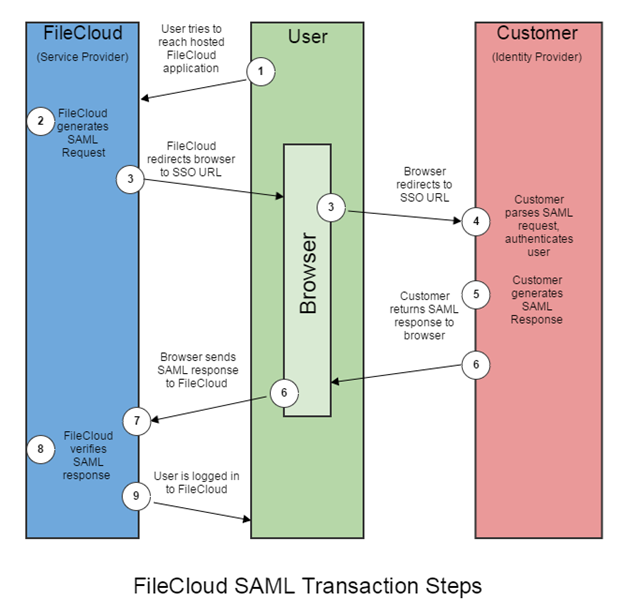
You can use SAML SSO to control the authorization and authentication of hosted user accounts that can access FileCloud Web based interface.
-
SAML is an XML-based open standard data format for exchanging authentication and authorization data between parties.
-
FileCloud supports SAML (Security Assertion Markup Language) based web browser Single Sign On (SSO) service
-
FileCloud acts as a Service Provider (SP) while the Customer or Partner acts as the identity provider (IdP). FileCloud SAML SSO service is based on SAML v2.0 specifications.
SSO Configuration Steps
In order to successfully configure SAML SSO, the following steps must be followed.
-
Configure Apache server by adding the Alias directive to the simplesaml.php configuration file.
Pre-requisite: The mcrypt module must be installed on the FileCloud Server.
In Windows, it should be installed by default.
In Linux, if mcrypt is not installed, it must be installed
To add the Alias directive:
The following are the typical entries in Linux and windows.
You can change these settings if the FileCloud is installed under a different WEB ROOT Folder
Windows
-
Navigate to the following directory
c:\xampp\apache\conf\extra -
Open the following file for editing
httpd-filecloud.conf -
Add the following line at the end of the file
Alias /simplesaml "/xampp/htdocs/thirdparty/simplesaml/public" -
Save the file.
-
Open the FileCloud Control Panel.
-
Use the control panel to stop and start the Webserver.
Ubuntu:
-
Open one of the the following files for editing:
/etc/apache2/sites-enabled/000-default.conf for HTTP (for port 80)
/etc/apache2/sites-enabled/default-ssl.conf for HTTPS (for port 443) -
Add the following line within <VirtualHost *:80> for HTTP connection or <VirtualHost *.443> for HTTPS connection. You can place it under the line DocumentRoot /var/www/html.
Alias /simplesaml /var/www/html/thirdparty/simplesaml/public -
To restart the apache webserver, run the following command:
service apache2 restart OR systemctl restart apache2
RHEL:
-
Open one of the the following files for editing:
/etc/httpd/conf/httpd.conf (for port 80)
/etc/httpd/conf.d/ssl.conf (for port 443) -
Add the following line within <VirtualHost *:80> for HTTP connection or <VirtualHost *.443> for HTTPS connection. You can place it under the line DocumentRoot /var/www/html.
Alias /simplesaml /var/www/html/thirdparty/simplesaml/public -
To restart the webserver, run the following command:
service httpd restart OR systemctl restart httpd
Troubleshooting
Override the default SSO port
To override the default port:
-
Open cloudconfig.php:
Windows Location: XAMPP DIRECTORY/htdocs/config/cloudconfig.php
Linux Location: /var/www/config/cloudconfig.php -
Add the following line:
define("TONIDOCLOUD_SSO_FULLURL_OVERRIDE", "https://filecloud.test.com");
Use multiple memcache servers
In FileCloud Versions 20.3.2 and higher, you can use multiple memcache servers with SAML SSO to achieve high availability.
To use multiple memcache servers:
-
Open cloudconfig.php:
Windows Location: XAMPP DIRECTORY/htdocs/config/cloudconfig.php
Linux Location: /var/www/config/cloudconfig.php -
Add the following lines, including a hostname for each of the memcache servers.
In this example, the IP addresses of the servers are 79.97.83.70 and 79.97.83.71.
function SSO_MEMCACHED_SERVERS() { return [ [ ['hostname' => '79.97.83.70'] ], [ ['hostname' => '79.97.83.71'] ], ]; }
In HA environments with SSO, either point all FileCloud server nodes to the same memcache server or to the same memcache cluster.
Any of the following will break SSO:
-
Pointing each FileCloud server node to the local memcache server, IP 127.0.0.1
-
Point each FileCloud server node to a different memcache server.
-